11 | Add to Reading ListSource URL: elections.utah.govLanguage: English - Date: 2018-03-19 15:40:19
|
|---|
12 | Add to Reading ListSource URL: gotechnica.orgLanguage: English - Date: 2018-10-24 21:42:12
|
|---|
13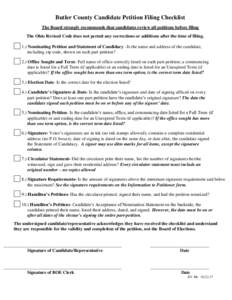 | Add to Reading ListSource URL: www.butlercountyelections.orgLanguage: English - Date: 2017-03-15 14:47:38
|
|---|
14 | Add to Reading ListSource URL: hacken.ioLanguage: English - Date: 2017-10-12 11:58:38
|
|---|
15 | Add to Reading ListSource URL: www.butlercountyelections.orgLanguage: English - Date: 2017-12-05 11:09:38
|
|---|
16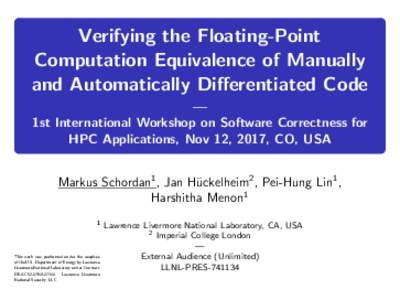 | Add to Reading ListSource URL: correctness-workshop.github.ioLanguage: English - Date: 2017-11-14 22:52:13
|
|---|
17 | Add to Reading ListSource URL: sos.alabama.govLanguage: English - Date: 2017-07-12 16:45:50
|
|---|
18 | Add to Reading ListSource URL: cakeml.orgLanguage: English - Date: 2018-05-16 23:20:58
|
|---|
19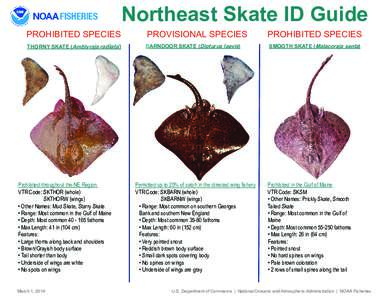 | Add to Reading ListSource URL: www.greateratlantic.fisheries.noaa.govLanguage: English - Date: 2018-10-15 10:36:08
|
|---|
20 | Add to Reading ListSource URL: hacken.ioLanguage: English - Date: 2017-10-12 11:58:32
|
|---|